
Salesforce Role Reductions Impact Agentforce, MuleSoft, Marketing Cloud
Salesforce has conducted a further round of layoffs, with notable reductions impacting employees in the...

Achieving successful Agentforce adoption hinges on organizational readiness, not just technical prowess. This guide outlines 10 best practices to ensure your...

Wildcards, NOT LIKE syntax, escaping, and bind-variable patterns with real Apex examples.

Profiles control what a user can do; roles control what they can see. The decision rules, simply.
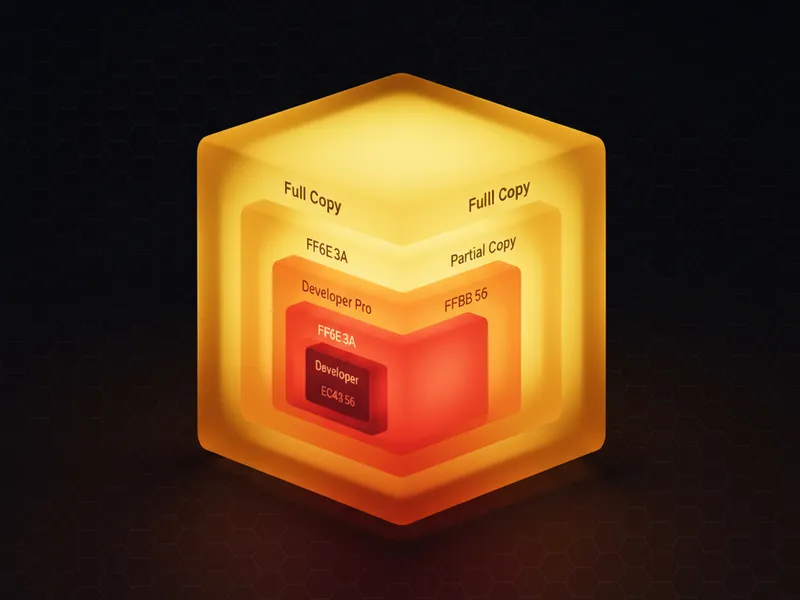
Compare Developer, Developer Pro, Partial Copy and Full sandboxes side-by-side.

Bulkification, trigger choice, fault paths, subflow design — the discipline that survives prod.

Step-by-step refresh, what gets wiped, and the recovery moves when something goes wrong.
WhoId points to people (Lead/Contact); WhatId points to records (Account/Opportunity).
Decimal vs Double, Long vs Integer, sObjects, collections — choose right the first time.

How VS Code talks to your org under the hood, and when to reach for it instead of Metadata API.

LightningModal vs custom — markup, parent-child events, focus trap, copy-paste code.

Prerequisites, the four required permissions, and the Setup toggle that turns it on.

Salesforce has conducted a further round of layoffs, with notable reductions impacting employees in the...
Salesforce's Zero Copy architecture evolved from Query Federation to File Federation to handle 120 trillion rows...
Salesforce's new President and CPO, Rohan Kumar, brings extensive experience from Microsoft, focusing on "ambient"...

Navigate the Salesforce Flow Builder interface and understand its core components like the Toolbox, canvas, and...
Historical technology adoption offers valuable lessons for implementing AI solutions. Understanding the long arc...
Technical debt is a persistent challenge in Salesforce orgs. This article outlines 10 practical strategies for...

Discover the five core Salesforce Flow types that can automate the vast majority of your business processes....

If you're attending the Agentforce World Tour London 2026, maximize your experience beyond the keynotes. Explore...
Salesforce Engineering 360 addressed operational challenges by unifying fragmented data across dozens of systems...
The Agentforce Conversation Client team leveraged AI-driven workflows and a custom MCP platform to automate...