
OAuth 2.0 JWT Bearer Flow: Packaging External Client Apps
Master the secure distribution of External Client Apps by mastering the JWT Bearer flow. We clarify the boundary...

Master the secure distribution of External Client Apps by mastering the JWT Bearer flow. We clarify the boundary...
Learn how Informatica modernized its single-node architecture into a distributed, Spark-based platform on...
A recent supply chain attack on the Axios HTTP client has created significant security risks for node.js-based...
This document outlines technical approaches for embedding Salesforce functionality, such as Screen Flows and LWCs,...
Developers migrating to Marketing Cloud Next face significant challenges unifying CRM Lead data with Marketing...
Salesforce has set February 28, 2028, as the retirement date for the Open CTI framework, necessitating...

This analysis evaluates the necessity of Proof Key for Code Exchange (PKCE) in OAuth 2.0 flows, particularly for...
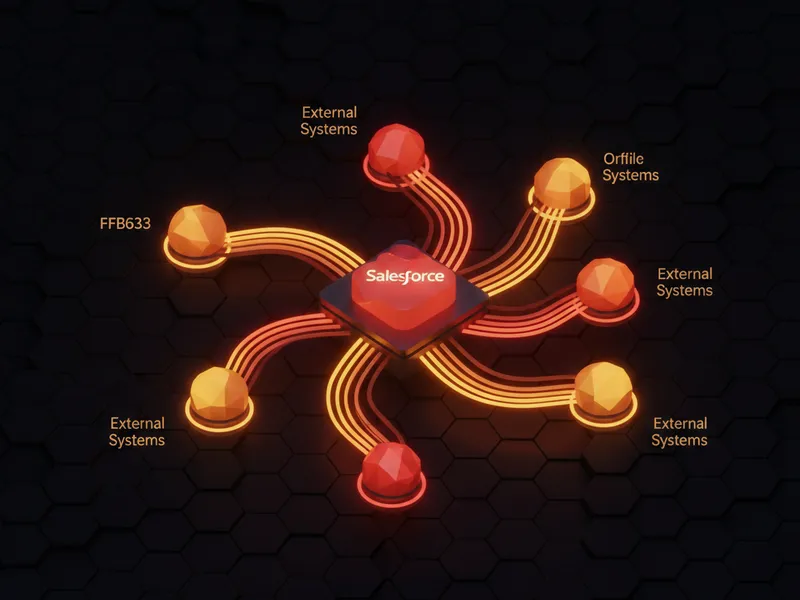
Selecting the right Salesforce integration platform requires assessing architectural fit, governance needs, and...
Examine common technical hurdles encountered in complex Salesforce architectures, focusing on automating...

Automating access token retrieval for numerous sandbox test users is a common CI/CD hurdle when testing as...

Choosing between a legacy SOAP tool and a modern event bus is a common architect dilemma. I break down the...
